Welcome to 2026. If you’re a business owner, a CTO, or a hiring manager, you already know that the digital landscape has shifted beneath our feet. The days of "off-the-shelf" software being "good enough" are long gone. Why? Because generic software comes with generic vulnerabilities. In a world where AI-driven cyber-attacks are the new normal, bespoke software development isn't just about getting a custom UI: it’s about building a digital fortress tailored to your specific needs.
At Chimpare, we’ve seen the evolution of threats firsthand. Whether you are scaling a fintech app or modernizing an enterprise ERP, security is no longer a checkbox at the end of the project. It is the foundation.
In this deep dive, we’ll explore the 10 essential security insights you must consider when embarking on a bespoke development journey this year. From quantum-resistant encryption to the psychology of Zero Trust, here is how you stay ahead of the curve.
Table of Contents
- Custom Security Architecture: Building the Skeleton
- Industry-Specific Controls: The End of One-Size-Fits-All
- Foundational Compliance: GDPR and Beyond in 2026
- AI-Enhanced Threat Detection: The Adaptive Shield
- Quantum-Resistant Encryption: Future-Proofing Data
- Shift-Left Testing: Fixing Bugs Before They Breathe
- Hardened Secure Coding Practices
- Data Sovereignty and Granular Access Management
- Automated Real-Time Compliance Monitoring
- The ROI of Security: A Business Necessity
- Common Security Mistakes in Bespoke Projects
- Bespoke vs. Off-the-Shelf: Security Comparison
- FAQ: Technical Security Queries
1. Custom Security Architecture: Building the Skeleton
When you choose bespoke software development, you aren't just buying code; you’re designing an ecosystem. In 2026, the most successful projects define their security architecture before a single line of functional code is written. This means integrating access levels, encryption standards, and authentication processes that are unique to your organizational risks.
Speciality: Architectural Hardening
Release Date: Q1 2026 (Modern Standards)
Key Features:
- Microservices isolation to prevent lateral movement.
- Customized API gateways with rate limiting tailored to user behavior.
- Hardware-level security integration for mobile applications.
Problem: Generic software uses a standard "house" layout that burglars already have the blueprints for.
Solution: Bespoke architecture creates a custom-designed vault where only you know where the secret passages are.
2. Industry-Specific Controls: The End of One-Size-Fits-All
A healthcare app built with Flutter app development requires vastly different security protocols than a retail loyalty platform. In 2026, bespoke software allows you to implement custom security protocols that match your industry’s specific threat profile.
- Fintech: Requires multi-layered transaction signing and "man-in-the-middle" protection at every node.
- Healthcare: Focuses on HIPAA-compliant data masking and immutable audit logs for patient records.
- Logistics: Needs secure IoT integration to prevent supply chain spoofing.
By tailoring controls, you avoid the bloat of unnecessary security features that slow down performance while ensuring the critical areas are triple-locked.
3. Foundational Compliance: GDPR and Beyond in 2026
Compliance isn't just a legal hurdle; it’s a trust signal. In 2026, data privacy regulations have become more fragmented and stringent. Bespoke software allows you to bake region-specific regulations (like the updated UK GDPR or the EU's AI Act) directly into the foundation of the product.
Speciality: Regulatory Engineering
Key Features:
- Privacy by Design: Data minimization techniques are automated.
- Right to Erasure: Automated workflows for "Right to be Forgotten" requests.
- Cross-Border Controls: Software that automatically adjusts data handling based on the user's geolocation.
If you are looking at Python development for data-heavy applications, building these compliance modules early saves millions in potential fines.
4. AI-Enhanced Threat Detection: The Adaptive Shield
Static firewalls are a relic of the past. In 2026, bespoke systems utilize AI-enhanced threat detection. These systems don't just look for known "bad" signatures; they learn your users' "normal" behavior. If a user in London suddenly attempts to download 5GB of data from a 2026 Node.js environment at 3 AM via a VPN, the system doesn't just flag it: it isolates the session instantly.
Speciality: Behavioural Analytics
Key Features:
- Machine learning models that adapt to new attack vectors in real-time.
- Zero Trust Architecture (ZTA) where every request is verified, regardless of origin.
- Automated incident response that "self-heals" compromised modules.
Problem: Traditional security alerts create "notification fatigue," causing teams to miss real threats.
Solution: AI filters the noise, handling 99% of minor anomalies autonomously so your team can focus on the big picture.
5. Quantum-Resistant Encryption: Future-Proofing Data
The "Quantum Apocalypse" might still be on the horizon, but the "harvest now, decrypt later" threat is real today. Hackers are stealing encrypted data now, intending to crack it once quantum computing becomes mainstream.
In 2026, bespoke software development should prioritize Post-Quantum Cryptography (PQC). This involves using cryptographic algorithms (like lattice-based cryptography) that are thought to be secure against a quantum computer attack. This is especially vital for long-term data storage solutions like those seen in our CS Prime Choice Security projects.
6. Shift-Left Testing: Fixing Bugs Before They Breathe
Industry data shows that a bug caught during the development phase costs nearly 10 times less to fix than one found after launch. In 2026, we utilize "Shift-Left" testing. This means security testing happens at every stage of the lifecycle: from ideation to deployment.
Speciality: DevSecOps Integration
Key Features:
- SAST/DAST: Static and Dynamic Application Security Testing integrated into the CI/CD pipeline.
- AI-Augmented Testing: AI agents that generate thousands of "edge case" scenarios to stress-test the code.
- Peer Reviews: Human-led code audits focused specifically on logic flaws that AI might miss.
Whether you're building with Swift or Kotlin, continuous testing ensures your software is born secure.
7. Hardened Secure Coding Practices
Quality bespoke development relies on developers who speak the language of security. At Chimpare, our engineers follow strict secure coding practices to mitigate common risks like SQL injection, Cross-Site Scripting (XSS), and Broken Access Control.
Security Specification List:
- Input Validation: Never trust user input; sanitize everything.
- Output Encoding: Prevent malicious scripts from executing in the browser.
- Dependency Management: Regularly auditing third-party libraries (a major vector for attacks in 2026).
- Secret Management: Using secure vaults (like HashiCorp Vault) rather than hardcoding API keys.
8. Data Sovereignty and Granular Access Management
In 2026, where you store your data and who can see it is a major business differentiator. Bespoke software gives you absolute control over data access management. Unlike SaaS platforms where the provider might have "backdoor" access, bespoke systems allow you to define exactly who has the keys to the castle.
Speciality: Identity and Access Management (IAM)
Key Features:
- Role-Based Access Control (RBAC): Users only see what they need for their specific job.
- Multi-Factor Authentication (MFA): Biometric and hardware-token integration as standard.
- Just-In-Time (JIT) Access: Granting elevated permissions only for the duration of a specific task.
For businesses looking to hire dedicated software engineers, ensuring they understand these IAM frameworks is critical for maintaining data sovereignty.
9. Automated Real-Time Compliance Monitoring
Manual audits are a thing of 2023. In 2026, bespoke platforms include dashboards that provide real-time regulatory alignment. If a new data privacy law is passed, or if a server configuration drifts from the "secure" baseline, you are notified immediately.
This is particularly useful for organizations using RPA development to handle sensitive back-office tasks. The bots themselves must be audited in real-time to ensure they aren't inadvertently exposing data.
Problem: Compliance is often a "once-a-year" snapshot that leaves you vulnerable for the other 364 days.
Solution: Continuous monitoring provides a 24/7 "heartbeat" of your security posture.
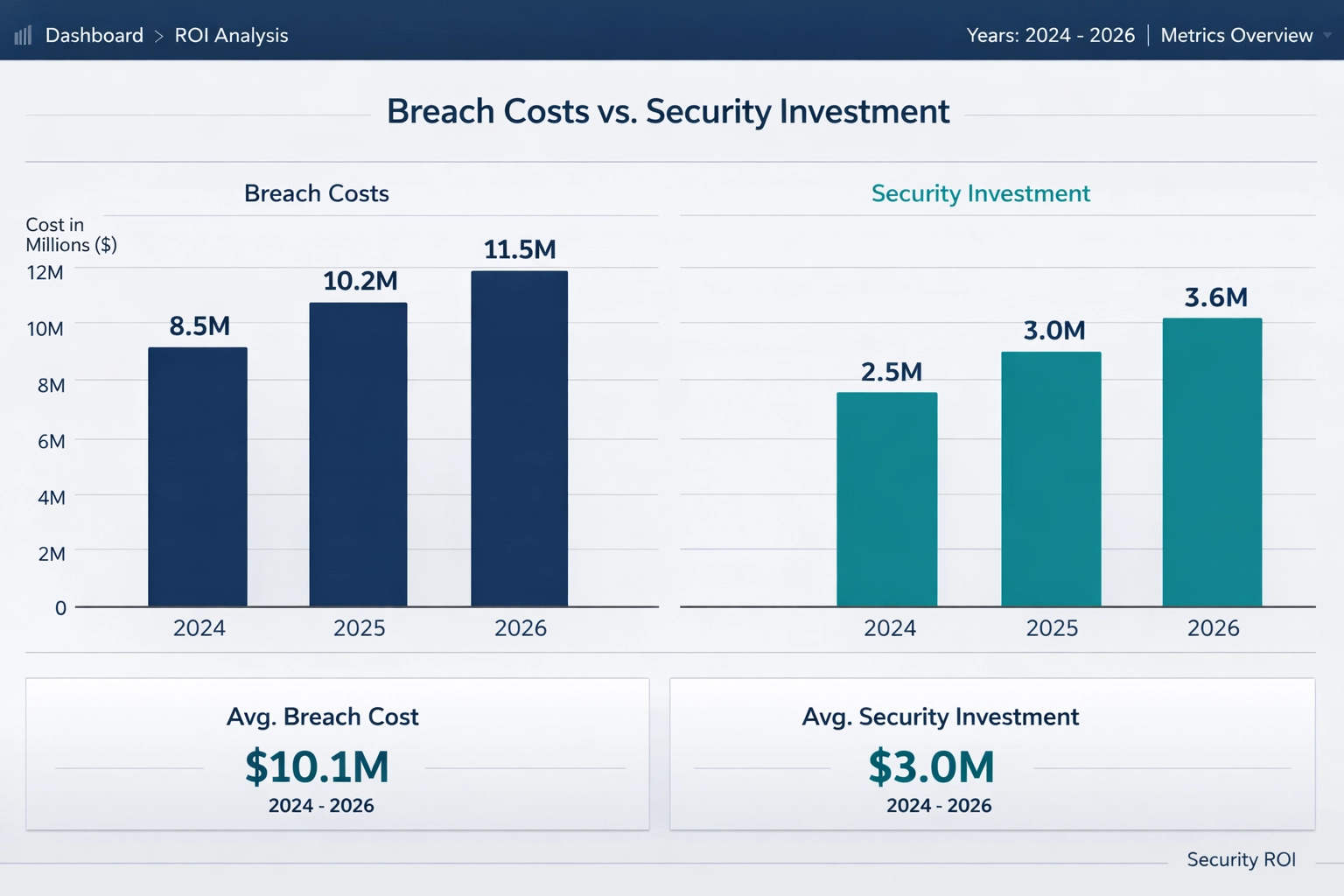
10. The ROI of Security: A Business Necessity
Investing in security isn't a cost; it’s an insurance policy with a high ROI. The average cost of a data breach has skyrocketed in the last few years, reaching well over $5 million for mid-sized enterprises in 2026.
The Business Value of Bespoke Security:
- Brand Trust: Customers are more likely to stay with a company that has a clean security record.
- Lower Insurance Premiums: Cyber insurance providers offer better rates for businesses with custom, hardened software.
- Competitive Advantage: Use your superior security as a selling point to your own clients.
Common Security Mistakes in Bespoke Projects
Even with a custom build, things can go wrong if the strategy is flawed. Here are the pitfalls we see most often:
- Neglecting API Security: Over 90% of organizations using APIs have suffered an incident. Insecure endpoints are the "unlocked windows" of the software world.
- Hardcoding Credentials: It sounds basic, but developers still occasionally leave "admin/admin" or API keys in the code during the rush to launch.
- Ignoring Technical Debt: Security requires updates. If you build a Laravel project and don't update the framework for two years, you’re asking for trouble.
- Over-Reliance on Third-Party Plugins: Every plugin is a potential vulnerability. Bespoke means building it yourself to keep the attack surface small.
- Poor Error Handling: Verbose error messages can give hackers clues about your database structure or server environment.
Visualizing the Security Landscape: Data Trends 2026
To understand why bespoke security is vital, let’s look at the projected costs of cybercrime versus the cost of proactive bespoke investment.
Cybersecurity Investment vs. Potential Breach Costs (2024-2026)
| Year | Avg. Cost of Breach (Global) | Avg. Bespoke Security Spend | ROI (Cost Avoidance) |
|---|---|---|---|
| 2024 | $4.45 Million | $150,000 | 29.6x |
| 2025 | $4.85 Million | $185,000 | 26.2x |
| 2026 | $5.30 Million | $210,000 | 25.2x |
Note: Data reflects industry trends in enterprise software sectors.
Bespoke vs. Off-the-Shelf: Security Comparison
| Feature | Off-the-Shelf (SaaS) | Bespoke Software Development |
|---|---|---|
| Vulnerability Profile | Publicly known; target of "mass" attacks. | Private; requires targeted, expensive effort to breach. |
| Compliance | General (e.g., standard GDPR). | Granular (Industry & Region specific). |
| Updates | Controlled by the vendor; you wait for them. | Controlled by you; patch as soon as a threat is found. |
| Data Access | Vendor has "super-user" access. | Absolute data sovereignty. |
| Integration | Limited; often requires insecure "middleware." | Seamless; security is baked into integrations. |
Choosing the Right Partner for Your 2026 Project
Selecting a partner for bespoke software development isn't just about finding the best coders. It's about finding a team that understands the 2026 threat landscape. When vetting a partner like Chimpare, ask these questions:
- Do you use AI in your testing process?
- How do you handle secrets management and encryption at rest?
- Can you demonstrate compliance with my specific industry standards (e.g., SOC2, ISO27001)?
- What is your process for managing third-party dependencies?
Forward-Looking Summary: Adaptation is Survival
As we move further into 2026, the gap between secure and unsecure businesses will widen into a canyon. Those who rely on generic, aging software will find themselves constantly playing catch-up with attackers who use the latest AI tools to find exploits.
Bespoke software development offers a way out. It allows you to build a system that is not only functional and beautiful but inherently resilient. By prioritizing custom architecture, AI-driven detection, and quantum-resistant standards today, you aren't just protecting your data: you’re protecting your future growth.
At Chimpare, we’re ready to help you build that future. Whether it's a React Native mobile app or a complex .NET enterprise system, we put security at the center of everything we do.
FAQ: Technical Security Queries
Q: Is bespoke software really more secure than big-name SaaS?
A: Yes and no. A poorly built bespoke app is worse than a well-maintained SaaS. However, a professionally developed bespoke app is significantly more secure because its codebase isn't public, making it much harder for automated "script kiddie" attacks to find vulnerabilities.
Q: How often should we conduct security audits in 2026?
A: With modern DevSecOps, "auditing" should be continuous. However, a deep-dive third-party penetration test should still be conducted at least twice a year or whenever major features are added.
Q: Does bespoke development take longer because of these security layers?
A: It requires more upfront planning, but it actually saves time in the long run. Fixing a security breach post-launch can take weeks of downtime and months of legal recovery. Building it right the first time is always faster.
Q: Can Chimpare help with migrating legacy data securely?
A: Absolutely. We specialize in secure data migration, ensuring that legacy vulnerabilities aren't carried over into your new bespoke system. Check out our work with Prime Choice Security for an idea of how we handle high-stakes environments.
Q: What is the most common entry point for hackers in 2026?
A: Compromised credentials and insecure APIs remain the top threats. That’s why we emphasize multi-factor authentication (MFA) and hardened API gateways in every project.